# SDN Controller
The SDN Controller enables a user to create pool-wide and cross-pool private networks and more. It's available as a Xen Orchestra plugin (included in XOA Premium).
# Global Private Networks
Interconnect your VMs and hosts within a dedicated and secured private network, even accross different pools all around the world. This is a great way to protect "private links" (eg between applications and databases, management networks etc.) without any complicated deployment.

# How does it work?
Please read the dedicated devblog on the SDN Controller (opens new window) and its extension for cross-pool private networks (opens new window).
WARNING
As VxLAN and GRE are protocols using extra encapsulation, they require extra bits on a network packet. If you create a Global Private Network with a default MTU at 1500, you won't be able to use it "as is" in your VMs, unless you configure a smaller MTU for each virtual interface, in your VM operating system (eg: 1400).
If you want something entirely transparent for your VMs, then you'll need to create a network with a MTU of 1546 for GRE or 1550 for VxLAN. However, larger MTU will require capable network equipments.
# Network creation
In the network creation view:
- Select a
pool - Select
Private network - Select an interface on which to create the network's tunnels
- Select the encapsulation: a choice is offered between
GREandVxLAN, ifVxLANis chosen, then port 4789 must be open for UDP traffic on all the network's hosts (see the requirements) - Choose if the network should be encrypted or not (see the requirements to use encryption)
- Select other
pools to add them to the network if desired- For each added
pool: select an interface on which to create the tunnels
- For each added
- Create the network
- Have fun! ☺

TIP
- All hosts in a private network must be able to reach the other hosts' management interface and all hosts must be able to reach one another on the interface selected for private networks creation.
The term ‘management interface’ is used to indicate the IP-enabled NIC that carries the management traffic.
- Only 1 encrypted GRE network and 1 encrypted VxLAN network per pool can exist at a time due to Open vSwitch limitation.
# Configuration
Like all other xo-server plugins, it can be configured directly via the web interface, see the plugin documentation (opens new window).
The plugin's configuration contains:
cert-dir: The path where the plugin will look for the certificates to create SSL connections with the hosts. If none is provided, the plugin will create its own self-signed certificates.override-certs: Enable to uninstall the existing SDN controller CA certificate in order to replace it with the plugin's one.
# Requirements
# VxLAN
- On XCP-ng prior to 7.6:
- To be able to use
VxLAN, the following line needs to be added, if not already present, in/etc/sysconfig/iptablesof all the hosts whereVxLANis wanted:-A xapi-INPUT -p udp -m conntrack --ctstate NEW -m udp --dport 4789 -j ACCEPT
- To be able to use
# Encryption
WARNING
Encryption is not available prior to XCP-ng 8.0.
- On XCP-ng 8.0:
- To be able to encrypt the networks,
openvswitch-ipsecpackage must be installed on all the hosts:yum install openvswitch-ipsec --enablerepo=xcp-ng-testingsystemctl enable ipsecsystemctl enable openvswitch-ipsecsystemctl start ipsecsystemctl start openvswitch-ipsec
- To be able to encrypt the networks,
# OpenFlow rules
Please see the devblog about OpenFlow rules (opens new window).
This feature requires the OpenFlow port to be opened
In the VM network tab a new column has been added: Network rules.
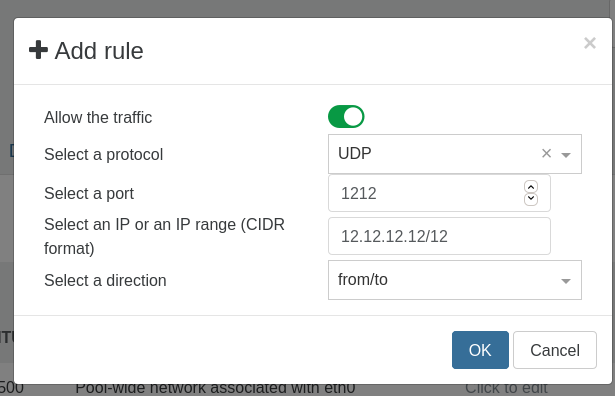
- The Add rule button display a form to add a new rule choosing to:
- enable/disable the matching traffic
- for a specific protocol (optional)
- on a specific port (optional)
- matching a specific IP or IP range (optional)
- coming from the VIF / going to the VIF / both
- The Show rules button allow to display all rules for a VIF.
- When the rules are display a button to delete a rule is available.

TIP
- This feature requires the OpenFlow port (TCP 6653) to be opened. (See the requirements)
# Requirements
# Openflow
- On XCP-ng prior to 8.0:
- To be able to use
OpenFlow, the following line needs to be added, if not already present, in/etc/sysconfig/iptablesof all the hosts whereOpenFlowis wanted:-A xapi-INPUT -p udp -m conntrack --ctstate NEW -m tcp --dport 6653 -j ACCEPT
- To be able to use
