XO 4.x starts to show up
ACLs, ACLs, ACLs! That's the rallying cry of our community since a long time. But we had to do a lot of work before even think on it. But yes, we take this time: our first draft was created nearly 1 year ago! This big feature will be the start of our new branch: the 4.x!
Concepts
People (e.g sysadmins) want to delegate VMs to other users (e.g developers), because it helps a lot to reduce the workload for them. There is a ton of use cases for delegating resources to others:
- could be inside (devs, devops, anyone who want to access its resources from a web browser)
- or outside (clients!).
That's not the only thing the community need: a self-service portal where you can create your VMs very easily is another requested possibility.
First step: first feedbacks
The first step is to provide a strong security model, right in the server xo-server, to avoid leaking any informations to the clients (xo-web or xo-cli). After that, we need to built around it our methods to connect to this model. And that's not the end! We also need to expose the features in the UI, to manage permission in your web browser.
Our initial work authorize an admin to delegate permissions to a user for specific objects (VMs, Storage Repo, hosts etc.).
This is where we are so far:
- our security model is implemented in
xo-server - we got a basic UI in
xo-web, allowing an admin to authorize a user to see a specific object - when this user is connected, he/she can only see authorized objects (VMs for example), and these only!
Here is actual video of this first step:
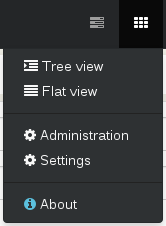
- go to the ACL view
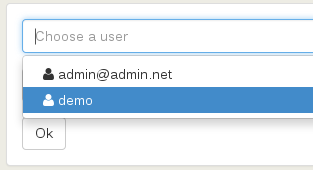
- choose the user you want to give permissions
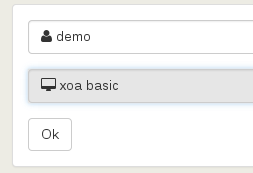
- select the object he/she will see and interact with (you can see we got live search in the select form)
Here is the workflow with screenshots:
Go the the Administration view:
Select the user:
Give him/her permission to see the object you want (in this case the VM xoa basic):
Done. You can remove the permission by clicking on the trash icon:
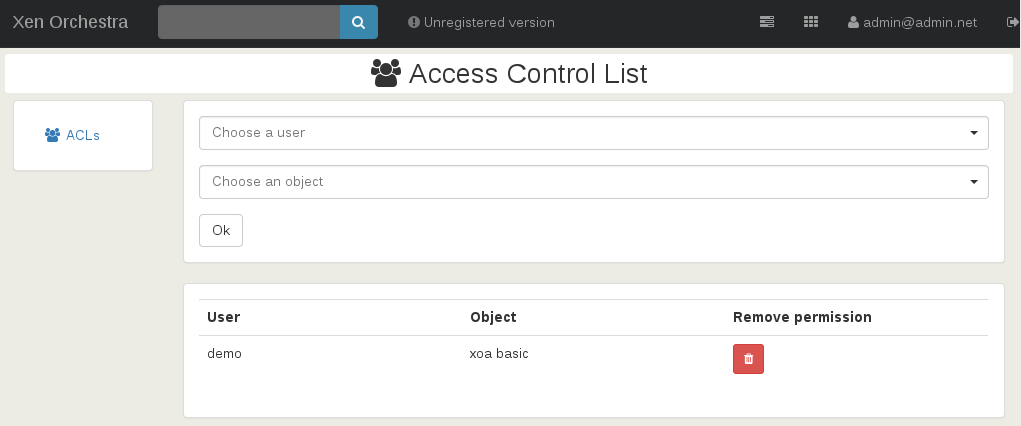
That's it! demo user will only see the VM xoa basic and nothing else.
After some feedback of our users, we should be able to go to the second step! But how to have a nice feedback?
- We'll start with a private beta with our existing clients, TODAY!
- Quickly after that, we'll offer XOA Enterprise on our web site, in a Early Access mode to everyone registering.
2nd step: complete ACLs
This time, the goal is to provide a better way to organize your permissions: groups, roles (respectively set of people and set of permissions) for objects. And finally, group of objects, aka VMs/SR/hosts etc. It should allow a great flexibility without increasing the complexity.
This also should be the step of connecting these ACLs to an external directory (Open LDAP or AD).
3rd step: self service
We'll probably create a specific permission, called "self-service", allowing those specific users to create themselves some VMs on designated hosts or pools. The current strategy in not very clear yet, but we'll have enough feedback from the previous steps to do that properly!
4th step: quotas
The last one is about to restrict users to drain too much resources from your hosts and pools, buy giving them quotas for each (e.g: vCPUs, RAM, Disk space, VIFs etc.)
When?
As I said previously, the first private Beta started to be sent to our existing clients. The official early access will be available NEXT WEEK! Hang on ;)