Xen security and XSA-108
You may have heard about Amazon or Rackspace rebooting some of their instances few days ago. It was known as a consequence of Xen Security Advisory number 108, aka XSA-108.
Update: the article is updated with more details and a correction about the amount of memory that could be read and privilege escalation.
Update 2: Xen Project Security Team release a very precise article on XSA-108. A must read if you want to know the details!
What it is
XSA-108 is also named "Improper MSR range used for x2APIC emulation". You can read more on the official announcement here. It affects only x86 architecture.
In short, if someone has administrator access to a guest (any DomU) running in HVM, he (or she) could crash the host or read any part some random part of the memory (up to 3KiB). This memory could be from another guest or the hypervisor itself.
That's why VPS vendors were very quick to deal with this problem. If combined with recent Bash security issue (shellshock), an attacker without any rights, could first get administrator access to a guest, and afterwards use XSA-108.
But to be clear, XSA-108 alone needs elevated guest OS privileges.
Bonus question:
- is PV guest impacted? No
- is PVHVM impacted? Yes.
How Xen people deal with security
Because Xen is used on major clouds on earth, the Xen team is very attentive to security concerns. They have a process well documented about their security policy (which you can read here).
XSA list
You can see anytime the list of XSA on this web page. Please not time are given in UTC.
But why Amazon know before me?
Because sometimes an advisory can be embargoed, due to its sensitive nature. Exactly like XSA-108! In this case, you need to be in the pre-disclosure list. It's well explained in the Xen security policy, but in short, you can apply if you want. Your application will be reviewed, depending on various standards (read the fine manual if you want to know more).
That's why Amazon and Rackspace (among others) were informed before the public statement.
Patching
Packaged Xen (Debian, CentOS)
Fix are already available, just run an upgrade from your favorite package manager. Example of the latest package in Debian Wheezy repo:
xen (4.1.4-3+deb7u3) wheezy-security;
* Security upload.
* Apply fix for Xen Security Advisory 108 (CVE-2014-7188)
* Apply fix for Xen Security Advisory 104 (CVE-2014-7154)
* Apply fix for Xen Security Advisory 105 (CVE-2014-7155)
* Apply fix for Xen Security Advisory 106 (CVE-2014-7156)
* Apply fix for Xen Security Advisory 56 (CVE-2013-2072)
Guido and Pasik (and other maintainers) were extremely fast to deliver those packages at the right time. Congrats guys!
XenServer
The XenServer team was also very reactive and ready to deliver on time. The patch is available here. You can patch it through xe-cli or XenCenter. Or soon, with Xen Orchestra. Oh, by the way, check this:
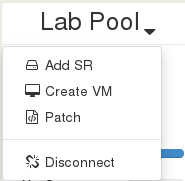
Yep, it's currently working and tested right now (we patched our servers with Xen Orchestra: it worked flawlessly).
The process is very neat: just click on "Patch", then select your *.xsupdate file and you're done. The patch will be uploaded, then applied on all your hosts in your pool without anything to do on your side. This stuff will be included soon in the next release.
From sources
If you are using Xen for sources, well, I won't explain how to apply a patch available in the XSA-108 ;)
Conclusion
Even if you have only PV guests, please consider patching: you'll never know if you'll test HVM or PVHVM later. It's also a very good habit to follow what's new in term of security advisories.
Don't forget that an attacker will never exploit only one vulnerability, but all he could find.
A big thanks to the Xen community for their reactivity. Do not hesitate to talk with them on the #xen irc channel on freenode.